DataPoints - National Data Commissioner Update August 2023
Participation in the DATA Scheme continues to grow – see our pipeline.
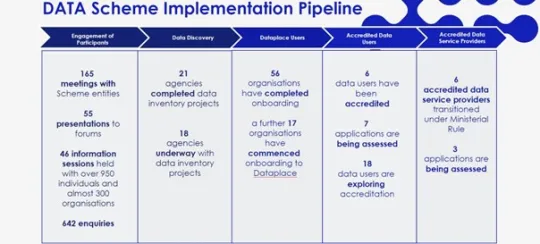
You can start your data journey by using our new guide to developing a data inventory. You can join the 56 organisations that have taken the step of onboarding to Dataplace. Once on board, you can use Dataplace to make a request for data collected by Australian Government agencies and make a data sharing agreement. Dataplace is also the place to go if you want to apply for accreditation to participate in the DATA Scheme. If you want to see who is already accredited, check out our Register of Accredited Entities.
Want to learn more about the DATA Scheme?
We are hosting webinars and online meetings throughout September for you to learn more about the DATA Scheme and strengthen your organisation’s data capability. Click the links below to register.
Join us on 7 September for:
Join us on 13 September for:
Join us on 14 September for:
New guidance to help Scheme participants
Under the DATA Scheme, Australian Government agencies may charge fees for services performed when dealing with a data sharing request under the DATA Scheme. Our new guidance requires that any fees charged are on a cost recovery basis.
One of the functions of the National Data Commissioner is to handle complaints about the DATA Scheme. To make a complaint, please go to our Contact us page or email information@datacommissioner.gov.au. Our new guidance provides information for Scheme participants and others about how the Commissioner will handle complaints.
National Data Advisory Council
Senator the Hon Katy Gallagher, Minister for Finance met with the National Data Advisory Council on 22 August to discuss the initial Data and Digital Government Strategy. You can read more about the Council’s work here.
Good reads for the data community
I had the pleasure of participating in the Life Course Centre’s Data for Policy Summit on 15-16 August. Two keynotes of interest - the Australian Statistician’s speech about the Australian Bureau of Statistics new Life Course Data Asset to help better understand and address communities experiencing entrenched disadvantage and Assistant Minister Andrew Leigh’s speech about the critical importance of data and evaluation.
Another good read is the Office of the Australian Information Commissioner’s Australian Community Attitudes to Privacy Survey. It shows a growing level of comfort with the government using personal information for research and service and policy development.
See also the Chief Scientist’s, Dr Cathy Foley, Trust in Science report. It describes the systems that underpin and support quality science in Australia.
Good uses of public data
We’re always looking to share great examples of how data can be used to improve the lives of Australians. Drawing on data from multiple sources, the Australian Institute for Health and Welfare’s recent report shows an interesting contrast between type 2 diabetes prevalence and incidence.
Almost 1.2 million (4.6%) Australians were living with type 2 diabetes in 2021 – a figure that is not getting smaller. But new diagnoses decreased by 43% between 2000 and 2021. This long-term declining trend, also seen in several other countries, might be due to improved preventive measures, including screening, increased awareness, educational programs, and changes in behaviour and risk factors.
If you’ve got feedback or something to share in future editions of DataPoints, please get in touch. We’re always interested to hear your stories, including about how you have used data to deliver public benefit.
Gayle